How CyberLab Executed Targeted Attack Simulations in Financial Services
Simulating Real‑World Attacks to Strengthen Financial Services Security
Financial services organisations operate in one of the most heavily targeted sectors globally. As threat actors continue to evolve their tactics, techniques and procedures, traditional security testing alone is no longer enough to provide confidence.
This case study explores how a leading UK financial services organisation partnered with CyberLab to validate its cyber defences through Red Teaming and targeted attack simulations, providing real‑world assurance that security controls, people and processes could withstand modern attack techniques.
Why Financial Services Are Prime Targets
Banks, lenders, building societies and financial services providers remain highly attractive to cyber criminals and advanced threat actors due to:
- High‑value financial data and assets
- Complex, interconnected digital environments
- Strict regulatory and compliance requirements
- Heavy reliance on customer‑facing digital services
Attackers increasingly combine technical exploitation with social engineering, targeting both systems and people. This makes realistic attack simulation a critical component of modern Cyber Security strategy.
About the Organisation
The organisation is a leading UK financial services provider, serving thousands of customers and members nationwide. Operating within a highly regulated environment, it has built a strong reputation based on trust, service excellence and regulatory compliance.
As part of an ongoing digital transformation programme, the organisation recognised that maintaining a resilient Cyber Security posture was essential to protecting customer data, financial assets and brand reputation.
To gain independent assurance of its security maturity, the organisation engaged CyberLab to conduct advanced offensive security testing aligned to real‑world attack scenarios.
How Are Cloud Services Treated Under the Updated Cyber Essentials Requirements?
The Business Challenge Financial services organisations face a dual challenge: enabling digital innovation while ensuring robust protection against increasingly sophisticated threats.
This organisation operated several business‑critical systems, including:
- Customer‑facing web and mobile banking platforms.
- Internal systems supporting lending and mortgage processes.
- Externally exposed infrastructure supporting digital services.
Any compromise could have resulted in:
- Unauthorised access to sensitive customer data.
- Operational disruption.
- Regulatory scrutiny and financial penalties.
- Long‑term reputational damage.
The organisation needed confidence that its preventative, detective and responsive controls would perform effectively under real attack conditions.
Why Red Teaming Matters in Financial Services
Unlike traditional penetration testing, Red Team exercises simulate the behaviour of genuine threat actors over an extended period.
For financial services organisations, Red Teaming helps to:
- Validate security controls across people, process and technology
- Test detection and response capabilities, not just prevention
- Identify gaps that only emerge during multi‑stage attacks
- Provide evidence of security maturity to regulators and stakeholders
This approach supports regulatory expectations around resilience, continuous improvement and proactive assurance.
The CyberLab Approach
CyberLab delivered a multi‑layered offensive security engagement, tailored to the organisation’s threat profile and risk priorities.
Red Team Exercise >
A multi‑week Red Team exercise simulated advanced attack techniques commonly used against financial institutions.
This included:
- Open‑source intelligence gathering
- Targeted spear‑phishing campaigns
- Assessment of user awareness and susceptibility to social engineering
- Attempts to gain initial access and escalate privileges
The objective was to mirror real‑world attacker behaviour and assess how effectively the organisation could prevent, detect and respond to an active threat.
External Infrastructure Testing >
CyberLab specialists conducted penetration testing across the organisation’s externally exposed infrastructure, assessing:
- Network‑level weaknesses
- Misconfigurations Vulnerabilities that could be exploited for unauthorised access
This testing helped identify technical gaps that attackers could leverage as entry points into the environment.
Web and Mobile Application Testing >
In‑depth testing of customer‑facing web and mobile applications was performed, aligned to the OWASP Top 10 where applicable.
Testing focused on:
- Authentication and authorisation controls
- Application logic flaws
- Data handling and exposure risks
Both automated and manual techniques were used to uncover issues that could impact customer trust and service availability.
The Outcome
The targeted attack simulation provided the organisation with clear, independent validation of its Cyber Security controls and overall resilience.
Key Outcomes
Validation of Cyber Security Controls
The organisation gained assurance that existing controls could defend against realistic attack scenarios.
Identification of Vulnerabilities
Technical and human‑centric weaknesses were identified, including areas susceptible to social engineering and control gaps that required attention.
Enhanced Security Posture
Actionable findings enabled targeted improvements to defensive controls, monitoring and incident response capabilities.
Clear Remediation Guidance
Comprehensive reporting provided prioritised recommendations, allowing efficient and effective remediation aligned to risk.
Key Takeaways for Financial Services Leaders
- Red Teaming provides insight that traditional testing cannot
- People remain a critical attack vector alongside technology
- Regulators increasingly expect evidence of realistic testing
- Continuous offensive testing supports long‑term resilience
Conclusion
Through an ongoing partnership with CyberLab, this financial services organisation continues to take a proactive approach to Cyber Security.
Regular Red Teaming and offensive testing enable the organisation to adapt to an evolving threat landscape, strengthen defences year on year and maintain the trust of customers and stakeholders.
By combining deep financial services expertise with real‑world attack simulation, CyberLab helps organisations protect what matters most: their people, their data and their reputation.
Ready to Explore Red Teaming?
If you want to understand how Red Teaming or targeted attack simulations could strengthen your organisation’s Cyber Security posture: Speak to a CyberLab expert today.
What is Penetration Testing? Everything You Need To Know About Security Testing
Everything You Need To Know
Penetration Testing, or a Pen Test, is a security test that launches a mock cyber attack to find vulnerabilities in a computer system.
A pen test is a way to identify vulnerabilities before attackers do, evaluate how effectively you can respond to security threats, assess your compliance with security policies, and improve the level of security awareness amongst your staff.
Penetration testers are security specialists trained in ethical hacking, using hacking methods and tools to identify and fix vulnerabilities rather than exploit them maliciously. Organisations purchase pen testing services to carry out simulated attacks on their applications, networks, and other systems. These controlled attacks enable security teams to discover serious weaknesses and strengthen their overall security defences.
While “ethical hacking” and “penetration testing” are sometimes used interchangeably, there is a subtle distinction. Ethical hacking is a broader discipline within cyber security that encompasses any application of hacking expertise to bolster security. Penetration testing, or pen testing, is one specific approach within ethical hacking, focusing on attack simulations. Ethical hackers may also offer malware analysis, risk evaluations, and other security-enhancing services.
Types of Penetration Testing
Penetration Testing
A Penetration Test aims to exploit the vulnerabilities of an organisation’s cybersecurity arrangements before a malicious party does. It uses a combination of automatic and manual techniques to identify issues within the infrastructure, systems and operations.
Vulnerability Assessment
Vulnerability Assessments are most often used by organisations when they want to identify the vulnerabilities present in their infrastructure and to get a high-level overview of their security posture. It involves an external approach and is fully automated.
Vulnerability Assessments are useful for companies who do not have visibility or understanding of their security posture. A vulnerability assessment can often be used as the first stage of a larger penetration testing project.
For organisations with legacy infrastructure, it is a quick, cost-effective way to identify and focus on software versions and systems that can be fixed easily.
External Penetration Test
An external penetration test replicates a real-life attack, searching for vulnerabilities that can be exploited by a hacker. This type of analysis aims to target everything Internet-facing. The penetration tester will focus on identifying network vulnerabilities. This can include issues with network services and hosts, devices, web, mail and FTP servers.
Objective Examples: Obtaining internal access to the network
Internal Penetration Test
An internal penetration test aims to identify and exploit internal vulnerabilities. Vulnerabilities can range from misconfigurations through to unpatched software and social engineering. The approach would be similar to an external penetration test, and the process followed would be the same.
Often the aim of this test can be unique to each client. A customer’s objective could be to gain access to a sensitive file or the domain controller with full admin rights, to elevate privileges or to perform an overall security assessment.
This type of test is only possible with access to the internal network either provided by the customer or gained by dropping a device like a dropbox or Raspberry PI onto any open network port, or by exploiting a compromised system i.e. emails.
Objective Examples: Leveraging internal access to obtain access to important assets on the network
Web Application Penetration Test
The web application penetration test aims to find weaknesses in applications programmed in-house or out of the box solutions, as well as ill-coded websites.
Web Apps are often vulnerable to many types of attacks that are often possible through the exploitation of misconfigurations in server builds or through bad coding practices. Vulnerabilities are often identified within functions where user input is received, like website search, address fields, file uploads, where SQL queries can be passed to gain access to back end databases. If either of those functionalists are not appropriately secured an attacker could exploit them to upload a malicious document that can create a back door giving a user unauthorised access to the underlying server it is running on.
Due to the world wide web being publicly exposed many websites and online stores come under constant attack. Identifying these vulnerabilities before anyone else can allows remediation actions to take place to secure the web app.
Examples: Brute-force attack, Error handling, SQL Injection and XSS.
Social Engineering
Social engineering is manipulating people into leaking sensitive information and providing an external malicious agent with unwarranted access to a network or building. It exploits the gaps in cyber security education in organisations and employs psychological persuasion.
The pen tester will research different aspects of the company and its people, refer to social media and current events, to gain the trust of the host and blend in with the organisation. However, social engineering is not limited to physical infiltration, but can also involve the use of email, social media and calls.
Performing such a test can reveal the gaps in cybersecurity awareness of the organisation’s people and stress the importance of employee training.
Examples: Phishing campaigns, traditional scamming techniques such as authority figure impersonation.
Red Team Engagement
A red team engagement is the more advanced version of a penetration test appropriate for companies with mature, well-established security arrangements. Compared to a pen test, they tend to take longer and often require multiple testers. The main objective is not to find and exploit all vulnerabilities, but instead, it is a targeted attack with a single objective aiming to be completely unnoticeable. Such tests are performed in scenarios where there is an immediate Blue team (Response Team) to stop a Red team (Attackers) in their tracks.
Black-Box Testing
In black-box testing, a tester doesn’t have any information about the internal working of the software system. It is a high-level assessment that focuses on the behaviour of the software. It involves testing from an external or end-user perspective. Black-box testing can be applied to virtually every level of software testing: unit, integration, system, and acceptance.
White-Box Testing
White-box testing is a testing technique which checks the internal functioning of the system. In this method, testing is based on coverage of code statements, branches, paths or conditions. White-box testing is considered as low-level testing. The white-box testing method assumes that the path of the logic in a unit or program is known.
Penetration Testing
Leave it to our team of expert penetration testers to identify vulnerabilities in your environment.
Our tailored assessments can cover every aspect of network security from general vulnerability identification to fully exploiting vulnerable web applications.
Vulnerability Assessment vs Penetration Test: Key Differences Explained
What Is The Difference & When To Use Each?
CyberLab explains how Vulnerability Assessments (VAs) and Penetration Tests (Pen Tests) work, how they complement each other, and how to build a sensible testing cadence that fits risk and change.
Quick Summary
- Vulnerability Assessment: Automated discovery of known weaknesses across systems and networks, producing a prioritised list to remediate. Fast coverage, broad visibility, highly repeatable.
- Penetration Test: Expert‑led simulation that chains weaknesses to achieve realistic attack objectives, validating impact and controls. Deeper insight, business‑level risk narrative, targeted improvements.
Both are essential. A VA finds what is exposed. A Pen Test proves what is exploitable and why it matters.
What is a Vulnerability Assessment?
A Vulnerability Assessment actively scans internal and/or external infrastructure to identify known weaknesses that attackers could exploit. It is run against defined IP ranges or assets and produces a report with findings and remediation guidance.
Typical issues uncovered include:
- Unpatched or end‑of‑life software
- Misconfigured or exposed services and ports
- Default or weak credentials (for example, admin/admin)
- Insecure protocols and ciphers (for example, legacy TLS versions)
Where it helps most:
- As the first step in a security testing journey, establishing a baseline quickly
- As a regular control to catch drift from secure baselines, configuration errors and newly disclosed vulnerabilities
Cadence: Monthly or quarterly is common, depending on change rate and risk appetite. Remember that VAs, like Pen Tests, provide a point‑in‑time view, so frequency matters.
Beyond automation: While scanning is largely automated, experienced teams add value with context, open‑source intelligence (OSINT) where appropriate, and aftercare that helps teams interpret, prioritise and fix efficiently.
What is a Penetration Test?
A Penetration Test goes further and deeper. It uses expert techniques to validate how vulnerabilities can be combined, exploited and escalated to achieve meaningful objectives.
Activities typically include:
- Research and reconnaissance
- Threat modelling and attack path analysis
- Vulnerability exploitation and privilege escalation
- Lateral movement and data access validation (within agreed scope)
- Documentation of impact with an executive summary, attack narrative, and ranked remediation plan
Cadence: Often annual as a baseline, with additional testing after significant changes such as new remote access solutions, major application releases or compliance drivers. Pen Tests are more resource‑intensive and take longer than VAs, which is why a staged approach is effective.
A Simple Analogy
Think of a network as a house.
- A Vulnerability Assessment identifies weaknesses: a rusty lock, a half‑open window, a bin that could be used as a step.
- A Penetration Test tries to chain these findings: test the lock, leverage the bin to reach the window, and prove whether a break‑in is possible.
Both insights are valuable. The VA shows where to improve. The Pen Test shows what really happens if issues are left unfixed.
Key Differences at a Glance
- Depth vs breadth: VA prioritises coverage and speed, Pen Test prioritises depth and realism.
- Automation vs expertise: VA is largely automated with expert interpretation, Pen Test is expert‑led throughout.
- Outcome: VA provides a list of weaknesses to remediate, Pen Test provides validated attack paths, business impact and targeted fixes.
- Frequency: VA more frequent to reduce exposure between changes, Pen Test periodic or change‑driven to validate resilience.
How They Work Together
- Start with a VA to remove the obvious and reduce the attack surface quickly.
- Follow with a Pen Test to validate critical paths, controls and detection/response.
- Repeat VAs regularly to catch configuration drift and new vulnerabilities.
- Trigger Pen Tests after major change or on a set cycle to keep assurance current.
What ‘Good’ Looks Like in the Reports
Vulnerability Assessment report:
- Clear asset scope and scan coverage
- Findings grouped and prioritised by severity, with fix guidance
- Trends over time when assessments are run regularly
Penetration Test report:
- Executive summary in business terms
- Attack narrative that explains how access was achieved and what it enabled
- Ranked vulnerabilities with technical detail and remediation steps
- Evidence that supports replication and verification
Both are only worthwhile if the organisation acts on remediation and tracks closure.
Practical Testing Cadence
- High change or internet‑facing assets: VA monthly, or more frequently for critical services
- Broad internal estate: VA quarterly
- Pen Test: annually as a baseline, plus after significant architectural or application change, or when required by regulation
Plan windows carefully. Automated scans can be “noisy” on the network, and some Pen Test activities may require coordination to avoid operational disruption.
Choosing a Trusted Provider
Look for independent, accredited testing delivered under strict NDAs and with clear separation from sales and implementation teams. Frameworks such as CREST help ensure quality, ethical practice and consistent methodology. Vendor‑agnostic reporting and unbiased recommendations support better decision‑making.
Getting Started
CyberLab helps organisations plan a sensible testing programme, starting with rapid visibility through a Vulnerability Assessment and moving to targeted Pen Testing that validates real‑world risk. The team can also support prioritised remediation and help embed repeatable processes so improvements stick.
To discuss scope, cadence and outcomes that fit your environment and risk profile, the CyberLab team is available for an initial consultation.
Free Posture Assessment
Understand your security risks and how to fix them.
Take the first step to improving your cyber security posture, looking at ten key areas you and your organisation should focus on, backed by NCSC guidance.
Claim your free 30-minute guided posture assessment with a CyberLab expert.
Your CREST Accredited Penetration Test Report Explained Clearly
What Does a Good Penetration Test Report Cover?
Penetration Testing or Pen Testing is a crucial tool in your IT security toolbox. It provides a method for gaining assurance that an IT system or infrastructure is secure through the use of simulated tools and attacks that are used in the real world, to attempt to breach or gain access.
Gavin Wood, CEO at CyberLab, uncovers what a Penetration Test report should provide, including…
- What is Penetration Testing?
- What is a Penetration Testing Report and What Should it Contain?
- Prevention v Cure
What is the Purpose of a Penetration Test?
The purpose of a Penetration Test is to discover any risks and allow you or your security team to act on them before anyone else does.
Typically pen tests are used to identify the level of risk from any hardware or software vulnerabilities and or any configuration issues within your environment.
The output of a Pen Test is usually in the form of a report that will grade any issues or vulnerabilities found so that these can be addressed, and any gaps closed.
What is a Penetration Testing Report and What Should it Contain?
A Penetration Test report, details any threats or vulnerabilities found and the recommended remedial actions.
Threats and vulnerabilities will be ranked in order of criticality. The report will also contain an executive summary and attack narrative which will explain the risks in business terms.
A penetration test report should involve the following areas…
- Risk and Executive Summary
- Approach, Scope and Caveats
- Findings Summary and Remedial Advice
Risk Summary
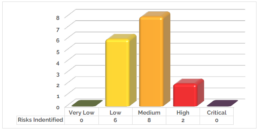
A risk summary details management and high level issues. These issues will be highlighted into 6 categories: Critical, high, medium, low, very low and informative.
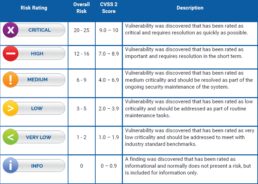
Executive Summary
A executive summary details management and high level issues, breaking down the report details to illustrate the level of risk that is exposed across the systems tested. This will highlight the total number of vulnerabilities identified during the assessment, along with their severity.
Approach, Scope and Caveats
This section introduces the in-depth reporting gathered from the Penetration Testing undertaken. It details the approach taken, the scope of engagement, and any limitations identified, such as, anything not attempted which could have risk of impact to service availability or system performance.
Findings Summary and Remedial Actions
The findings summary is where you can find the technical information regarding the assessment conducted. This section is broken down into: summary, technical details, recommendations and systems affected.

Prevention v Cure
With the risk of being controversial I am going to make an analogy between Pen Testing and vaccination.
We all know how vaccines work; they are a pre-emptive action against an illness to stop you getting the full affects and or be able counter the actual illness should you come in to contact with it.
A Pen Test is a pre-emptive action that allows you to discover and remediate any issues before someone else does.
Having a Pen Test should be part of your prevention strategy for IT security. Simply put you can’t manage what you can’t see, if you don’t know you have vulnerabilities, you cannot close them down. Pen Testing is an ideal way to give you the visibility of these issues and allows you to take remediation action to correct.
Given that cyber incidents are the 3rd biggest business risk for 2021* (that year’s top risk) and the average cost of remediating a ransomware attack now at $1.85 Million** prevention must be better than the cure!
However, Pen Testing is not a magic bullet, and it does have limitations; it’s a point in time test of the infrastructure. If a vulnerability is introduced after the pen test has been conducted it can still impact on your security. So regular testing is essential, especially after deploying new systems and technologies and as a part of your security continual improvement lifecycle.
Penetration Testing
Leave it to our team of expert penetration testers to identify vulnerabilities in your environment.
Our tailored assessments can cover every aspect of network security from general vulnerability identification to fully exploiting vulnerable web applications.


