Exploiting ChatGPT: The Darkside of AI and Emerging Cyber Threats
How Cyber Criminals Are Weaponising AI
Artificial intelligence (AI) being used for malicious intent has surfaced as a significant concern within the digital space. Cyber criminals are using Large Language Models (LLMs), like ChatGPT, and deepfake technology to launch cyber-attacks and scams. In this blog, we focus on the darker facets of AI, shedding light on the exploitation of AI systems, its impact on the threat landscape, and what organisations can do now to better protect themselves and their most sensitive assets against this new wave of threats.
Malicious ChatGPT Prompts for Sale on the Dark Web Marketplace
- Recent reports reveal a disturbing trend where thousands of malicious prompts designed to jailbreak and exploit AI are up for sale on the dark web. These prompts deceive AI models, enabling threat actors to steal data, orchestrate sophisticated scams and other illegal activities with alarming efficiency.
- According to recent research carried out by Kaspersky, thousands of these nefarious prompts and compromised premium ChatGPT accounts are now available for purchase, posing a significant threat to ChatGPT, its users and their data. (source: The Register)
Deepfake and AI: Partners in Crime
AI and deepfake technologies are becoming more readily available. OpenAI, for example, recently announced their new generative AI, Sora, that can create video from text. And, although this advancement in technology and its availability is exciting, it is also inevitable that there will be cyber criminals looking to use it maliciously.
Around the globe we are already seeing examples of these technologies being exploited by advanced threat actors, including cyber criminals, nation states or nation sponsored hacker groups.
$25 million theft executed through a sophisticated deepfake scam
A recent article by Ars Technica has shed light on a ground-breaking cyber crime incident considered to be the first successful heist of its kind: a $25 million theft executed through a sophisticated deepfake scam. The scam involved the creation of highly convincing AI generated deepfake videos, which were used to impersonate key individuals within a financial institution.
By leveraging these deepfake videos, the scammer manipulated employees into authorising fraudulent transactions, resulting in the substantial loss. This unprecedented heist marks a significant escalation in the sophistication of cyber criminal tactics, underscoring the evolving threat landscape faced by organisations worldwide. As the prevalence of AI-driven scams will inevitably continue to rise, it becomes increasingly crucial for businesses to bolster their cyber security posture and remain vigilant against such deceptive schemes.
Deepfake news segments
Iran-backed hackers had recently disrupted TV streaming services in the United Arab Emirates (UAE) by injecting deepfake news segments into the broadcasts according to The Guardian. These deceptive deepfake videos, generated using AI technology, were designed to resemble legitimate news reports, spread misinformation, and sow discord among viewers. This incident underscores the growing threat posed by state-sponsored threat actors and the increasing weaponisation of deepfake technology for political purposes.
As nations continue to grapple with the challenges of cyber warfare and disinformation campaigns, it becomes imperative for governments to collaborate and implement international legislation that both prohibits and protects against the use of such attack methods, as well as educate and inform organisations across all industries about AI threats and how best to protect themselves and their assets. Additionally, organisations need to enhance and adapt their cyber security capabilities to be able to identify and defend against orchestrated AI driven attacks, which is backed up by a recent assessment conducted by the NCSC. The assessment focuses on how AI will impact the efficacy of cyber operations and the implications for the cyber threat over the next two years. (source: NCSC)
Tales from the CyberLab: Generative AI in Cyber Security Explained
Global Cyber Threats Expected to Rise With AI, NCSC Warns
According to the above-mentioned assessment by the NCSC, AI is poised to significantly impact the cyber threat landscape in the near future. The report suggests that AI will almost certainly be utilised by cyber adversaries to enhance their capabilities, including the development of more advanced attack techniques and procedures (TTPs).
As AI technologies evolve, cyber criminals are increasingly going to automate tasks, evade detection, and execute targeted attacks with greater precision. This assessment underscores the urgent need for organisations to adapt their cyber security strategies to effectively mitigate the evolving threats posed by AI-driven cyber-attacks. This includes enhancing detection and response capabilities, investing in AI-powered security solutions, enforcing zero trust policies, implementing a culture of sufficient cyber awareness and vigilance amongst staff, and staying informed about emerging AI-driven threat vectors.
While ChatGPT and other LLMs may not yet be capable of being used to write sophisticated malware to be sold at scale on the dark web or be in possession of nefarious nation states, we may not be far away from AI being used to orchestrate attack chains or write malware that can evade detection. A separate recent report from the National Cyber Security Centre (NCSC) sheds light on how AI driven ransomware attacks could become a reality by 2025. (source: NCSC)
What Can Organisations do to Protect Themselves Against AI Threats?
As AI technologies are rapidly evolving, the application of its use for both good and bad is evolving with it, leading to a rapid shift in the threat landscape. It is imperative for organisations to not just understand how to defend against AI driven threats, but to learn how to use AI technologies securely and in a manner that best protects their assets and does not expose them to new vulnerabilities or risk.
Already we are seeing collaboration amongst the international community to tackle this very issue. A recent publication on how to engage with Artificial Intelligence has been developed by the Australian Signals Directorate’s Australian Cyber Security Centre (ASD’s ACSC) in collaboration with the NCSC, United States (US) Cyber security and Infrastructure Security Agency (CISA), Canadian Centre for Cyber Security (CCCS) and several other cyber security/government agencies from international partners. The publication highlights some key threats related to AI systems and summarises steps organisations should take when engaging with AI technologies (both in-house and 3rd parties) to mitigate risk. (source: ASD’s ACSC)
While this new wave of advanced threats seems daunting and paints a bleak future for stakeholders responsible for managing risk, there are several steps organisations can do to protect against these threats. Many of these types of attacks still rely on the presence of human error and social engineering. Regularly training your people and creating a positive cyber awareness culture are key to reducing this type of threat.
Further to this, unsecured vulnerabilities are a common route of entry for cyber criminals and can be identified with regular vulnerability scanning and penetration testing to identify your security weak spots.
Organisations across all sectors, of all sizes should not neglect the fundamental steps that make up the foundations of any cyber security strategy. Few organisations have the right tools, people, and processes in-house to manage their security program around-the-clock while proactively defending against new and emerging threats. Adopting security defences like Sophos MDR can provide an elite team of threat hunters and response experts to take targeted actions on your behalf to neutralise even the most sophisticated threats.
Tales from the CyberLab: AI’s Role in Data Protection Explained
In Conclusion
For better or worse, AI is going to change how we live our lives greatly, and while its application for solving huge problems on a global scale is something to be embraced, we should also be aware of its capacity to cause great harm. Organisations need to adapt to the new world of AI driven technologies and attacks, whilst continuing to invest in the foundations of their cyber security posture.
Free Posture Assessment
Understand your security risks and how to fix them.
Take the first step to improving your cyber security posture, looking at ten key areas you and your organisation should focus on, backed by NCSC guidance.
Claim your free 30-minute guided posture assessment with a CyberLab expert.
Mobile Security Threats & How To Protect Yourself from Common Risks
Your 2025 Guide to Mobile Threats and Defences
Adam Myers, Sales Director at CyberLab, outlines the evolving mobile threat landscape and offers actionable advice to help organisations and individuals secure their mobile devices.
Mobile devices are now central to business operations. According to Microsoft, over 80% of daily work is conducted on mobile platforms. These devices operate outside traditional corporate firewalls and are often in the hands of users who may not prioritise security – making them prime targets for cyber criminals.
Why Mobile Security Matters More Than Ever
Employees routinely access emails, documents, customer data, and applications via mobile devices. While this boosts productivity, it also increases exposure to threats such as malware, phishing, and data breaches.
The rise of Bring Your Own Device (BYOD) policies and remote work has further complicated mobile security management.
Top Mobile Security Threats in 2025
1. Outdated Operating Systems and Security Patches
Devices typically stop receiving updates within 3–4 years of release. Unpatched vulnerabilities are a leading cause of mobile breaches. Microsoft’s Secure Future Initiative urges organisations to retire outdated systems before they become liabilities.
2. Unsecured Third-Party Apps
Apps downloaded outside official stores (e.g. sideloaded APKs on Android) can introduce malware. These apps may access sensitive data, including passwords and banking details, without user awareness.
3. Weak Passcodes
Simple passcodes like “1234” or birthdates are easily guessed. Best practice now recommends 8-digit passcodes with no repeating patterns. Biometric authentication and phishing-resistant MFA are also strongly advised.
4. Unsecured Wi-Fi Networks
Public Wi-Fi remains a major risk. Attackers can intercept unencrypted traffic or hijack sessions. Microsoft recommends avoiding public networks unless using a trusted VPN.
5. BYOD Risks
Personal devices used for work can introduce threats if not properly managed. Risks include data theft, unauthorised app downloads, and lack of visibility into device security posture.
6. Lack of Endpoint Protection
Endpoint protection is no longer optional. Sophos and Microsoft now offer AI-powered threat detection and response for mobile endpoints, including behavioural analysis and automated containment. [microsoft.com]
7. Device Loss or Theft
EE reports that 10 million work devices are lost annually. Mobile Device Management (MDM) solutions allow remote wiping, location tracking, and access revocation to mitigate this risk.
8. Human Error
Employees remain a top vulnerability. Regular training and phishing simulations are essential. CyberLab’s layered security approach includes education, monitoring, and proactive threat hunting.
Mobile Device Management (MDM): Your First Line of Defence
An MDM solution helps organisations:
- Remotely wipe or lock lost devices
- Enforce strong passcode policies
- Ensure OS updates are applied
- Restrict access to risky apps
- Manage BYOD securely
MDM is cost-effective, easy to deploy, and scalable. CyberLab offers tailored MDM solutions—from entry-level setups to enterprise-grade deployments—based on your business needs.
Tales from the CyberLab: Cyber Security for Websites & Applications Explained
CyberLab Can Help
Speak with a CyberLab expert to review your mobile security posture and explore solutions tailored to your organisation. Book your free 30-minute consultation today.
Free Posture Assessment
Understand your security risks and how to fix them.
Take the first step to improving your cyber security posture, looking at ten key areas you and your organisation should focus on, backed by NCSC guidance.
Claim your free 30-minute guided posture assessment with a CyberLab expert.
Five Essential Cyber Security Measures: Practical Cyber Security Tips
Practical Cyber Security Tips Every Small Business Should Know
With the increasing frequency and sophistication of cyber attacks, it is crucial for SMEs to adopt robust cyber security practices to safeguard their business and data.
This blog focuses on essential cyber security best practices tailored for SMEs, highlighting key resources and actionable steps to protect your business.
Cyber Security Best Practices for SMEs
Implementing effective cyber security measures doesn’t require a massive budget or extensive expertise.
Employee Training and Awareness
Educate your staff about common cyber threats such as phishing, malware, and social engineering. Regular training sessions can help employees recognise and avoid potential security risks.
Strong Password Policies
Encourage the use of strong, unique passwords for all accounts. Implement multi-factor authentication (MFA) wherever possible to add an extra layer of security.
Regular Software Updates: Keep all software, including operating systems and applications, up to date with the latest security patches. Regular updates help protect against known vulnerabilities.
Data Encryption
Encrypt sensitive data both in transit and at rest. This ensures that even if data is intercepted or accessed without authorisation, it remains unreadable.
Backup and Recovery Plans
Regularly back up your data and ensure that backups are stored securely. Test your recovery plan to ensure that you can quickly restore operations in the event of a cyber incident.
Gain Cyber Essentials
Achieving Cyber Essentials certification demonstrates your commitment to cyber security and provides a solid foundation for your security practices.
Understanding Cyber Essentials
Cyber Essentials is a UK government-backed certification scheme led by IASME, designed to help organisations of all sizes protect against common online threats.
The scheme covers five key areas:
- Firewalls and Internet Gateways: Implementing firewalls to secure your internet connection.
- Secure Configuration: Ensuring that systems are configured securely to reduce vulnerabilities.
- Access Control: Managing user access to data and services to minimise risk.
- Malware Protection: Installing and maintaining anti-malware solutions.
- Patch Management: Keeping software up to date with the latest security patches.
By adhering to these principles, SMEs can significantly reduce their risk of cyber attacks and improve their overall security posture.
Actionable Steps for SMEs
Here are additional steps small businesses can take to protect themselves from cyber threats.
Conduct Regular Security Audits
Periodically review your organisation’s security posture, taking a holistic approach that assesses to identify and address any vulnerabilities or gaps. There are several, open-source industry standards and security frameworks available online that organisations, including SMEs, can align to such as NIST, CIS Critical Security Controls SME Companion, and NCSC. CIS even offers a free Controls Self-Assessment Tool (CIS CSAT) to help you get started.
Vulnerability Management
Regularly identify, assess, and mitigate vulnerabilities in your systems. Using Cyber Security as a Service (CSaaS) solutions, such as HackRisk, can help you stay on top of vulnerabilities without the need for a dedicated in-house team
Develop an Incident Response Plan
Prepare for potential security incidents by creating a response plan. Outline procedures for detecting, responding to, and recovering from cyber-attacks. Sophos offers a free incident response planning guide which can be downloaded here.
Utilise Cloud Security Solutions
Many cloud service providers offer robust security features that can help SMEs protect their data and applications.
Outsource to Experts
If maintaining an in-house cyber security team is not feasible, consider outsourcing to a dedicated team of experts. Services such as those offered by Sophos provide ongoing support and incident response capabilities, alleviating some of the cost and resource burdens.
Communication Protocols
Establish clear protocols for communicating internally and externally during a security incident. This ensures that information is disseminated quickly and accurately, minimising confusion and mitigating damage.
Free Posture Assessment
Understand your security risks and how to fix them.
Take the first step to improving your cyber security posture, looking at ten key areas you and your organisation should focus on, backed by NCSC guidance.
Claim your free 30-minute guided posture assessment with a CyberLab expert.
Identity and Access Management: Controlling Access in a Digital World
Controlling Access in a Digital World: Why IAM Matters More Than Ever
Identity and Access Management, often shortened to just IAM, is the practise of ensuring that identity of who and what is accessing your environment is under control – that is, you have systems and, by association, data that can only be accessed by users and devices that you have authorised.
But it’s a lot more than just that, in any organisation people come and go, it is also about making sure that when users (or devices) should no longer be authorised to access your systems that they are not still able to do so.
It sounds simple, but in a busy organisation it is easy for simply disabling a user account to be forgotten. Removing access for users or devices is a vitally important step in any cyber security strategy, especially under unfortunate circumstances when people leave a business on bad terms.
Identity and Access Management is a crucial aspect of cyber security. It involves controlling who and what can access your systems and data. Access to data, systems, and services need to be protected. Understanding who or what needs access, and under what conditions, is just as important as knowing who needs to be kept out.
Why do we need Identity and Access Management?
Data is the lifeblood of any business; in any digital organisation today it is a critical component in maintaining business as usual operation, theft, access denial or destruction of data is not only disruptive, but without good backups it can be devastating at scale.
The next step is controlling access to the data. Any organisation will have sensitive data, and that data is sensitive for a reason, it would likely be detrimental to the business if lost or released publicly. Ensuring the data is only accessible to parties that are trusted and need to access the sensitive data is another essential part of Identity and Access Management.
Implementing Identity and Access Management
Which brings us to the how. In modern IT the term identity encompasses much more than just the user account in active directory, there can be multiple associated devices the instantaneous status of which can be leveraged to provide additional security. For example, you could consider whether a device is managed by the organisation? What is the patch status of a laptop? Is the mobile device jail-broken or rooted?
The steps below are suggestions on things that can be done, they are by no means exhaustive and not every step is applicable or appropriate for every organisation; but by implementing these elements you can have confidence that you are doing IAM right:
Identity and Access Management Policies
Organisations should look to develop appropriate IAM policies and processes.
- Control who and what can access your systems and data. A good IAM policy that covers who should have access to which systems, data or functionality, why, and under what circumstances.
- Consider all potential types of user including full and part-time staff, contractors, volunteers, students, and visitors.
- Ensure the policy covers what and how audit records are acquired, and how they are safeguarded against tampering, and an identification of which actions or processes, if any, should require more than one person to perform or authorise them.
- Policies should not just cover systems you control, but also wherever your organisational identities can be used – for example, consider the websites or online services that staff can create an account by using their work email address.
Login Methods
Establish and prove the identity of users, devices, or systems, with enough confidence to make access control decisions. Single sign-on (SSO) may be available using your organisational identity for some online services to help you control access to those services (and revoke access along with someone’s work account when they leave your organisation).
New Starters, Movers and Leavers
Ensure your account management processes include a ‘joiners, movers and leavers’ policy, so access can be revoked when no longer needed, or changed for movers. Temporary accounts should also be removed or suspended when no longer required.
In Conclusion
By following these steps, you can ensure that only individuals and systems that are authorised to have access to data or services are allowed to do so. This will result in less impact on staff’s workday by getting IAM right across an organisation, smoother collaboration with customers, suppliers, and partners.
Free Posture Assessment
Understand your security risks and how to fix them.
Take the first step to improving your cyber security posture, looking at ten key areas you and your organisation should focus on, backed by NCSC guidance.
Claim your free 30-minute guided posture assessment with a CyberLab expert.
How to Prevent Cyber Attacks with Effective Logging and Monitoring
Detecting and Preventing Cyber Incidents
- Why Do We Need Logging and Monitoring?
- How Do We Do Logging and Monitoring?
- Identifying the Right Solution
- Our Recommendations
Why Do We Need Logging & Monitoring?
The dark web has been hugely commoditised and it is now very likely that multiple cyber criminals will gain awareness that you are vulnerable. This happens when one attacker, called an access broker, gains access to your environment and then sells that access to multiple other attackers. Their goal? Making money, causing chaos, stealing secrets, and holding your data hostage.
The risk and cost for organisations that are victim to cyber attacks are also increasing. The result of cyber attacks are often downtime, disruption and data loss. There are also other consequences many organisations face such damage to reputation, hefty fines for compromised data, losing trust from valued customers, and even the loss of hard-earned certifications.
While it might seem like a digital doomsday out there, here’s the secret: cyber attacks leave footprints. The art of prevention lies in spotting these traces before the attack compromises your systems and data. It’s like catching a thief in the act before they can make off with the loot. If you can detect unauthorised activity before damage is done, you can stop or prevent the attack being successful and limit the damage. That’s where logging and monitoring solutions come in.
They have a secondary function as well, anyone who has suffered a cyber attack will tell you that despite having the initial detection of something untoward going on, it can be really difficult to actually feel confidence that you can see the whole picture and you are aware of everything that’s going on – logging and monitoring helps with that as well.
How Do You Do Logging & Monitoring?
In even relatively small IT environments, the scale of log information that will be generated is overwhelming. Especially if it’s scattered across multiple environments like public/private cloud/SaaS etc.
The first challenge? Gathering all these pieces into a single, meaningful picture. Endpoint Detection & Response and eXtended Detection and Response (EDR/XDR) and Security Information and Event Management (SIEM) solutions provide this central location to collate and view the log information from multiple sources.
So, you’ve got all your puzzle pieces in one place, but they’re still just random bits until you put them together. That’s where the real magic happens: processing. EDR/XDR and SIEM solutions typically sift through the sea of data to block out the ‘noise’.
Solutions such as LogPoint leverage some form of AI or ML intelligence to give an indication of how likely a particular event is going to be related to malicious activity. LogPoint’s version is called UEBA, which stands for User Entity Behaviour Analytics. UEBA uses AI and ML to correlate multiple events and link related ones together to give a fuller picture than looking at individual events in isolation.
EDR/XDR solutions usually do something similar but typically the events they are correlating are limited to information coming from endpoint security or proprietary network devices. LogPoint and other SIEM tend to have a much broader scope of interoperability and call pull event information from pretty much anywhere that it’s being generated.
How Do I Know Which Solution Is Right?
It can be difficult to know which solution is right for your organisation, and its often a case of selecting which fulfils your need the best. If you don’t need to monitor extensive hardware devices, web sites, databases, etc, then an EDR/XDR solution might be for you. If you have multiple databases or databases that hold sensitive information, it’s probably a good idea to be watching them closely via a SIEM solution as they will be a prime target for an attacker.
With both types of solution the information still needs to be monitored by a human. LogPoint mitigate this through the use of their Security Orchestration and Response (SOAR) technology that aims to take automated action based on certain triggers when particular activity is detected. EDR/XDR solutions often have similar functionality but it’s probably fair to say they are not quite as extensive or complex as a SIEM solutions.
These automated response solutions are great, but they can also be incredibly disruptive if allowed free reign over systems. Very quickly users will be complaining they cannot carry out their duties because things are being blocked. This brings me to the final challenge with logging and monitoring, it invariably means a security specialist with “eyes-on-glass” (i.e., watching the screen) is necessary to manage both types of solutions effectively.
Again, the approach to take to manage this final challenge depends on any number of factors – the size of business, the driving forces behind the adoption of logging and monitoring, the desire for Opex over Capex, or the constant problem of getting skilled Cyber security staff, to name just a few.
What Would CyberLab Recommend?
If an organisation lacks in-house expertise but recognises the value and importance of logging and monitoring, it is increasingly common to adopt a managed service approach.
This involves partnering with third-party suppliers who have dedicated security specialist teams to handle the heavy lifting. One of the key benefits of this approach is peace of mind – knowing that systems are being actively protected around the clock.
To support this, the Posture Assessment tool offers a quick and easy way to identify strengths and weaknesses, providing a clearer picture of overall security posture.
A dedicated page of recommendations for improving logging and monitoring is available, including guidance on which tools can help.
For organisations looking to strengthen their security and protect their data, a consultation with one of our experts is available to explore tailored solutions.
Free Posture Assessment
Understand your security risks and how to fix them.
Take the first step to improving your cyber security posture, looking at ten key areas you and your organisation should focus on, backed by NCSC guidance.
Claim your free 30-minute guided posture assessment with a CyberLab expert.
Vulnerability Management for Stronger Cyber Security Resilience
Protect Your Data. Secure Your Organisation.
Our host discusses the key elements of vulnerability management and shares how to protect your organisation through robust practices and monitoring.
He covers:
- What is vulnerability management?
- Why do we need vulnerability management?
- Key steps to vulnerability management
What is Vulnerability Management?
Vulnerability management is the process of identifying and addressing weaknesses in computer systems, networks, and software that could be exploited by hackers or cause security breaches.
It involves regularly scanning and assessing these systems to discover any vulnerabilities or potential entry points for attacks.
Once identified, these vulnerabilities are prioritised based on their severity, and appropriate measures are taken to fix or mitigate them.
Why Do We Need Vulnerability Management?
By actively managing vulnerabilities, organisations can reduce the risk of cyber attacks and safeguard their sensitive information from unauthorised access or damage.
Software Updates
Software might be fine at the time it is released, but as time and requirements move on, the code of the software does too. This could be to add cool new features or to add a flashy new interface, but it’s becoming more important to fix security issues or vulnerabilities. These issues can be found either by security testers known as ‘Bug bounty’ hunters or the software vendor themselves.
Fixing these vulnerabilities prevents cyber-attacks from exploiting them. According to a recent report by the Ponemon Institute, more than half (57%) of reported data breaches could have been avoided if known vulnerabilities had been patched correctly.
What are the Risks of Not Updating?
Keeping outdated software can be a big risk for an organisation – it’s like leaving your door unlocked. A study by the Centre for Strategic and International Studies revealed that cybercrime costs the global economy more than $1 trillion each year, with a significant portion resulting from data breaches.
The rising cost of cyber insurance is another risk that organisations need to consider. Companies that neglect proper vulnerability management practices often face higher cyber insurance premiums, Cyberpolicy estimates that companies without basic patch management measures in place may face cyber insurance premiums up to 25% higher.
Key Steps to Vulnerability Management
Gain Visibility
Scanning internally and externally with vulnerability assessment tools can highlight network layer “low hanging fruit” vulnerabilities that hackers will be looking to find the quickest and or least detectable entry point into an organisation’s network. According to a study by Spiceworks, 72% of IT professionals use vulnerability scanning tools to identify and remediate security risks.
Identify Risk
To effectively manage vulnerabilities, you need to identify and eliminate areas of risk, such as unsupported operating systems, hardware, and applications. Essentially, anything connected to your internal infrastructure and external interfaces adds to this risk. According to a report by Tripwire, 76% of respondents identified legacy systems as the main challenge to their security.
Secure Your Websites
Knowing which web applications are accessible to the public via web browsers is crucial for your cybersecurity strategy. Protecting externally facing web applications that hold sensitive data (such as PII, PHI, PCI data, or commercially sensitive/customer data) is vital.
Performing regular vulnerability scans and at least one manual penetration test per year helps organisations address new vulnerabilities. It also helps to prevent unauthorised access to sensitive data, compromised user accounts, or external threats with increased privileges that could cause further harm.
Protect Your Data
In today’s world, attackers primarily target your data. They aim to either steal it, deny you access to it, or both, with the goal of extorting money from your organisation.
When you consider how your data can be accessed, you can identify potential sources of risk and develop a strategy to minimise those risks. This involves considering vulnerabilities and controls, such as limiting access to authorised individuals, to protect your data effectively.
Addressing Your Vulnerabilities
It may seem obvious, but patch management is often overlooked or delayed, leading to future problems. Investing in reliable and effective automated patch management solutions is the best approach. While they may cost more, they require less constant tweaking and management, giving you confidence in their effective patching.
Identifying problems is often straightforward, but finding solutions can be challenging, especially when dealing with legacy or unsupported mission-critical operating systems or applications that cannot be shut down.
Scheduled downtime is crucial to apply security fixes to these systems. If they are attacked without fixes in place, you’ll face unscheduled downtime, which is worse. If downtime or security fixes are not feasible, alternative solutions like Forescout can be used to implement effective network access controls and restrict access to vulnerable areas only to authorised entities.
Utilise Reporting
Managing vulnerabilities at a large scale is impractical as it would require constant effort to find and fix issues. Automation is the key to making it feasible. Reporting can be used to identify existing issues before applying patches and to verify the effectiveness of the patching process. Most solutions offer automated reports that range from high-level summaries to detailed breakdowns of vulnerabilities.
How CyberLab Can Help
CyberLab can provide consultancy and support on your key technology projects, help deliver business solutions, support your users in adopting them and provide managed or reactive support when your solution is up and running.
Free Posture Assessment
Understand your security risks and how to fix them.
Take the first step to improving your cyber security posture, looking at ten key areas you and your organisation should focus on, backed by NCSC guidance.
Claim your free 30-minute guided posture assessment with a CyberLab expert.
The Top Five Cyber Threats of 2024 and How to Strengthen Resilience
Mid-Year Analysis on Cyber Security Trends for 2024
As we progress through 2024, the cyber threat landscape continues to evolve rapidly, presenting new challenges for organisations and individuals alike. In this edition, we shift our focus from past incidents to the present and future threats that pose the greatest risks.
Understanding these threats is crucial for developing effective strategies to safeguard against them. Cybercrime is expected to become the world’s third largest economy by 2025, estimated to cost $10.5 trillion in damages globally, according to cybercrime magazine.
This month, we highlight the top five most dangerous cyber threats of 2024, exploring their nature, potential impacts, and the steps you can take to protect yourself and your organisation. Join us as we explore these pressing cyber threats and provide insights into enhancing your cyber resilience.
Offensive AI as a Threat Multiplier
At the RSA Conference 2024, cyber security experts identified offensive AI as a significant threat multiplier, presenting it as one of the top five cyber threats for the year. Stephen Sims highlighted how malicious actors leverage AI and automation to rapidly identify vulnerabilities, automate the generation of exploits, and launch sophisticated attack campaigns.
This offensive AI capability accelerates the discovery and exploitation of vulnerabilities, posing a formidable challenge for defenders. Sims emphasised the urgent need for defensive strategies capable of countering the speed, automation, and intelligence wielded by attackers, underscoring the importance of innovative defensive measures to mitigate this evolving threat landscape in 2024.
AI-Driven Social Engineering Threats
Social engineering has long been a prominent cyber threat, relying on psychological manipulation to deceive victims. Attackers exploit human traits such as trust, fear, and curiosity to gain access to critical systems or sensitive information. Traditional social engineering methods include phishing, baiting, pretexting, and tailgating.
The increasing digital transformation and real-time information sharing have made individuals more susceptible to these attacks. In 2022 alone, there were 493 million ransomware attacks, and 19% of all data breaches were due to stolen or compromised login credentials.
AI has significantly amplified social engineering tactics, enabling attackers to develop more complex and convincing attacks tailored to targeted individuals. AI-driven social engineering can include:
- Hyper-personalised phishing
- AI-generated natural language content
- Emotional manipulation
- Detection evasion
- Automated reconnaissance
These advancements allow attackers to craft tailored, context-aware campaigns quickly and efficiently, making traditional defences less effective. Businesses must now contend with AI-generated deepfakes, persuasive phishing emails, and sophisticated data manipulation, requiring a proactive and adaptive approach to cybersecurity.
Implementing multi-factor authentication, employee training, phishing simulations, and AI-based defence mechanisms are essential to counter these advanced threats.
Ransomware Remains a Prevalent Threat in 2024
Despite significant global law enforcement efforts, ransomware activity has continued to surge in 2024. According to the Sophos 2024 Ransomware Report, global ransomware attacks in 2023 set a record high, surpassing the previous year by nearly 70%. In the first quarter of 2024 alone, 1,075 ransomware victims were posted on leak sites. Major ransomware groups like LockBit and ALPHV/BlackCat were responsible for 30% of the activity.
The report also highlights the financial impact of these attacks, with average ransom payments increasing by 500% in the last year. A staggering 63% of ransom demands were for $1 million or more, and 30% exceeded $5 million, indicating that ransomware operators are targeting larger payoffs.
Overall, these reports indicate that ransomware isn’t slowing down in 2024 and remains one of the largest threats to organisations. Few organisations have the right tools, people, and processes in-house to manage their security program around-the-clock while proactively defending against new and emerging threats.
Supply Chain Risk: A Growing Concern
Supply chain risk continues to be a significant threat in 2024, as we’ve already seen from major incidents this year involving MoD and MITRE, which we covered in our blog outlining the top five cyber incidents of 2024 so far. Despite increased awareness, many businesses still struggle with effectively managing these risks. According to the UK Government’s Cyber Security Breaches Survey 2024, 31% of businesses and 26% of charities conducted cyber security risk assessments in the past year. Larger organisations are more proactive, with 63% of medium businesses and 72% of large businesses conducting these assessments.
However, only 11% of businesses review the cyber risks posed by their immediate suppliers, a figure that rises to 28% for medium businesses and 48% for large businesses. This limited oversight is concerning given the complex and interconnected nature of modern supply chains. The qualitative data indicates that while awareness of supply chain cybersecurity risks is growing, smaller organisations often lack the formal procedures necessary to manage these risks effectively.
Cloud Vulnerabilities: The Invisible Threat
As organisations continue to migrate their operations to the cloud, vulnerabilities within cloud environments have become a critical concern in 2024. The flexibility and scalability of cloud services come with a unique set of security challenges that can be exploited by well-versed threat actors.
A significant factor contributing to cloud vulnerabilities is misconfiguration. According to reports as far back as 2019, misconfigured cloud settings were responsible for nearly 70% of all cloud security incidents, and according to IBM’s Cost of a Data Breach Report, 45% of reported breaches were cloud-based. These misconfigurations can lead to unauthorised access, data leaks, and compliance issues. Additionally, the shared responsibility model of cloud security often leads to confusion about where the provider’s security obligations end and the client’s responsibilities begin, leaving gaps that can be exploited. The NCSC has published free guidance on cloud security and shared responsibility models.
The rise in cloud-based attacks has also been driven by increasingly sophisticated threat actors targeting cloud infrastructure. For instance, the recent breaches involving high-profile cloud services such as the recent Microsoft Azure incident have shown that attackers are leveraging advanced techniques and exploiting zero-day vulnerabilities to bypass security controls, escalate privileges, and access sensitive data. These incidents highlight the importance of robust security practices, including regular audits, comprehensive monitoring, and strict access controls.
To mitigate cloud vulnerabilities, organisations should focus on improving their cloud security posture through continuous monitoring to identify any vulnerabilities or misconfigurations exposing their cloud infrastructure’s attack surface, employee training and implementing robust policies for access, user groups and data handling, and of course, adherence to best practices for cloud configuration and management. The Center for Internet Security (CIS) has published the CIS Benchmarks, a series of prescriptive recommendations for configuring over 25 cloud and network vendor product families including AWS, Azure and Google Cloud Platform (GCP).
By addressing these vulnerabilities proactively and implementing industry best practices and benchmarks, businesses can better protect their data and maintain trust with their customers.
What Can We Learn From These Trends?
The top five cyber threats of 2024 so far serve as a stark reminder of the evolving threat landscape. By understanding the risk and implementing a layered and strategic approach to cyber security, organisations can better protect their people, data, and customers.
Free Posture Assessment
Understand your security risks and how to fix them.
Take the first step to improving your cyber security posture, looking at ten key areas you and your organisation should focus on, backed by NCSC guidance.
Claim your free 30-minute guided posture assessment with a CyberLab expert.
Strategies to Strengthen Your Cyber Resilience for Hybrid Working
Key Considerations in a World of Hybrid Work
A recent survey by Forbes found that 63% of respondents worked remotely or in a hybrid model, showcasing that even years after the COVID 19 pandemic, hybrid working remains the norm. The importance of securing employees and the systems they access, whether they are working in the office or remotely, cannot be understated.
In this blog, we discuss distributed nature of hybrid working, the risks and cyber threats that hybrid working organisations are exposed to, alongside some recommendations and best practices that organisations can implement for securing hybrid and remote working environments.
Remote and Hybrid Working in the UK: Before and After the Pandemic
According to a report by the Wales Institute of Social and Economic Research and Data (WISERD) just 4.7% of UK employees worked from home in 2019, prior to the COVID-19 pandemic. However, by April 2020, 46.6% of employees did at least part of their job from home, and in 2022, a quarter of all UK employees worked in hybrid environments and 13% were working fully remotely.
The speed and scale at which the pandemic shifted a significant portion of UK’s workforce to hybrid/remote working, underscores the massive increase in cyber threats and incidents that followed, and the challenges that businesses and organisations would need to address in order to adapt. [source: ONS]
Cyber Threats and Risk Implications for Hybrid Working
Cyber attacks Up 238% Since the Pandemic
According to a study by Alliance Virtual Offices, the frequency of cyber attacks has surged by 238% since the shift to widespread remote working, largely driven by vulnerabilities in home networks and personal devices. Remote work has also increased the cost of data breaches for companies by an average of £104,077 (converted from $USD). Despite this, only 56% of remote employees receive regular cyber security training, increasing the risks for organisations operating in a more digital environment. [source: Yahoo Finance]
BYOD and Home Networks Expand Attack Surface
Research from Lookout found that 32% of remote workers use apps not approved by their company’s IT department, and 90% access corporate networks from multiple locations, including coffee shops and public Wi-Fi, which increases cyber risk. This can also increase exposure to threats like phishing and malware attacks, especially as 46% of employees save work files on personal devices. [source: IT Security Guru]
Common Attack Vectors – An increase in RDP Abuse
In light of so many organisations migrating to remote/hybrid working models, threat actors have turned their sights to exploiting remote/virtual desktop technologies as a means of bypassing external defensive parameters and gaining a foothold on the internal network.
Remote desktop protocol (RDP) is a common method for establishing remote access on Windows systems. According to a recent report by Sophos found that cyber criminals abused remote desktop protocol in 90% of attacks. This was the highest incidence of RDP abuse since Sophos began releasing its Active Adversary reports in 2021, covering data from 2020.
Remote Work Security Gaps
Cyber security experts also warn that hybrid work models expose companies to new risks. Remote workers that use unsecured personal devices and networks are a target for cyber criminals as they increasingly target collaboration apps like Slack and Teams to launch social engineering attacks. With the introduction of faster 5G networks, attacks on mobile devices are also expected to rise, as noted by UpGuard.
Cyber Threats and Risk Implications for Hybrid Working
The evolution of digital security is now at a pivotal point. The old models, based on clear boundaries between “inside” and “outside,” no longer hold. IT and InfoSec teams now have to contend with much greater digital attack surfaces, endpoint and firmware management challenges and company-wide adherence to remote/hybrid working policies.
A Forrester study in 2023, found that remote and hybrid working models has magnified IT operational challenges for 75% of participating organisations. Below are some best practices and essentials for secure remote/hybrid working models:
Implement Strong Access Controls
Organisations must ensure that only authorised users can access corporate systems. This includes multi-factor authentication (MFA) and device authentication, which requires pre-registering devices before allowing network access. Zero-trust security models that continuously verify user identities and devices are also highly recommended for hybrid environments (Security Boulevard).
Adopt Zero Trust Architecture
Zero Trust is an architectural approach where inherent trust in the network is removed, the network is assumed hostile, and each request is verified based on an access policy. By implementing a “never trust, always verify” approach to network security, requiring continuous authentication and least-privilege access to ensure that every request—whether from inside or outside the network—is fully verified before access is granted, organisations can significantly reduce lateral movement from possible threat actors and improves security across cloud, on-premises, and hybrid environments. NIST has published further guidance on Zero Trust Architecture here.
Develop and Enforce a BYOD Policy, Using Encryption and Backups
Clear policies for using personal devices for work must be established, covering security measures such as mandatory installation of security software and limiting personal use on company devices, while limiting the amount of access through personal devices. This minimises the risk of unauthorised access and data leakage.
Encrypting all stored data on devices used for remote work adds an extra layer of protection in case of theft or unauthorised access. It’s also essential to back up important data regularly, ensuring it can be restored in the event of a cyber attack or system failure. Additionally, enabling remote wipe capabilities for lost or compromised devices ensures sensitive data can be erased quickly.
Use Secure Networks and Tools
Remote workers should avoid public Wi-Fi where possible due to its high vulnerability. Instead, they should rely on personal hotspots or secure VPNs, which encrypt data and protect it from potential attackers on unsecured networks. Similarly, using secure video conferencing platforms and company-approved email systems helps reduce the risk of unauthorised access to communications.
Regular Penetration Testing and Red Teaming
Penetration testing and Red Team exercises are crucial for identifying vulnerabilities across their external and corporate networks, applications or devices before attackers can exploit them. By conducting Targeted Attack Simulations (TAS) or Red Team exercises that simulate exploiting vulnerabilities or gaps in remote/hybrid working environments companies can evaluate their overall security posture of their remote working infrastructure and focus resources on vulnerable areas to improve their defences against such attack vectors.
Regular Software Updates and Endpoint Protection
Ensuring that all devices, including personal ones used for work (BYOD), have up-to-date antivirus and firewall protection is crucial.
Regularly updating and patching software, coupled with continuous vulnerability assessments, is vital for maintaining a secure infrastructure. Cyber security as a Service (CSaaS) solutions, such as HackRisk, can help companies manage vulnerabilities effectively without overburdening internal teams.
Phishing and Social Engineering Awareness Training
Employees are often the first line of defence against cyber threats. Regular training sessions on phishing, social engineering, and secure data handling can significantly reduce the risk of human error leading to a security breach
Managed Detection and Response (MDR)
Endpoint detection alone is no longer sufficient given today’s digital threat landscape. Organisations must now employ an “always-on” threat detection and monitoring capability. However, employing and retaining qualified cyber security analysts, engineers can very expensive and hard to come by, let alone the continuously high costs of using XDR and SIEM technologies. Running a 24/7 SOC (Security Operations Centre) in-house with experienced analysts and security experts with state-of-the-art defensive technologies are typically reserved for multi-national conglomerates and banks.
MDR services (Managed Detection and Response) provide continuous monitoring and analysis of an organisation’s entire estate, including endpoints, network traffic and activity logs. By outsourcing to experts, firms can ensure that threats are detected and mitigated in real-time, reducing the risk of a successful attack.
Free Posture Assessment
Understand your security risks and how to fix them.
Take the first step to improving your cyber security posture, looking at ten key areas you and your organisation should focus on, backed by NCSC guidance.
Claim your free 30-minute guided posture assessment with a CyberLab expert.
Your CREST Accredited Penetration Test Report Explained Clearly
What Does a Good Penetration Test Report Cover?
Penetration Testing or Pen Testing is a crucial tool in your IT security toolbox. It provides a method for gaining assurance that an IT system or infrastructure is secure through the use of simulated tools and attacks that are used in the real world, to attempt to breach or gain access.
Gavin Wood, CEO at CyberLab, uncovers what a Penetration Test report should provide, including…
- What is Penetration Testing?
- What is a Penetration Testing Report and What Should it Contain?
- Prevention v Cure
What is the Purpose of a Penetration Test?
The purpose of a Penetration Test is to discover any risks and allow you or your security team to act on them before anyone else does.
Typically pen tests are used to identify the level of risk from any hardware or software vulnerabilities and or any configuration issues within your environment.
The output of a Pen Test is usually in the form of a report that will grade any issues or vulnerabilities found so that these can be addressed, and any gaps closed.
What is a Penetration Testing Report and What Should it Contain?
A Penetration Test report, details any threats or vulnerabilities found and the recommended remedial actions.
Threats and vulnerabilities will be ranked in order of criticality. The report will also contain an executive summary and attack narrative which will explain the risks in business terms.
A penetration test report should involve the following areas…
- Risk and Executive Summary
- Approach, Scope and Caveats
- Findings Summary and Remedial Advice
Risk Summary
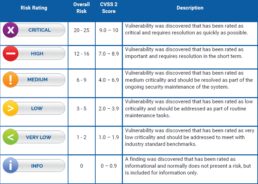
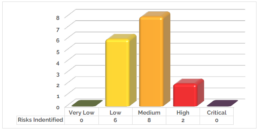
A risk summary details management and high level issues. These issues will be highlighted into 6 categories: Critical, high, medium, low, very low and informative.
Executive Summary
A executive summary details management and high level issues, breaking down the report details to illustrate the level of risk that is exposed across the systems tested. This will highlight the total number of vulnerabilities identified during the assessment, along with their severity.
Approach, Scope and Caveats
This section introduces the in-depth reporting gathered from the Penetration Testing undertaken. It details the approach taken, the scope of engagement, and any limitations identified, such as, anything not attempted which could have risk of impact to service availability or system performance.
Findings Summary and Remedial Actions
The findings summary is where you can find the technical information regarding the assessment conducted. This section is broken down into: summary, technical details, recommendations and systems affected.

Prevention v Cure
With the risk of being controversial I am going to make an analogy between Pen Testing and vaccination.
We all know how vaccines work; they are a pre-emptive action against an illness to stop you getting the full affects and or be able counter the actual illness should you come in to contact with it.
A Pen Test is a pre-emptive action that allows you to discover and remediate any issues before someone else does.
Having a Pen Test should be part of your prevention strategy for IT security. Simply put you can’t manage what you can’t see, if you don’t know you have vulnerabilities, you cannot close them down. Pen Testing is an ideal way to give you the visibility of these issues and allows you to take remediation action to correct.
Given that cyber incidents are the 3rd biggest business risk for 2021* (that year’s top risk) and the average cost of remediating a ransomware attack now at $1.85 Million** prevention must be better than the cure!
However, Pen Testing is not a magic bullet, and it does have limitations; it’s a point in time test of the infrastructure. If a vulnerability is introduced after the pen test has been conducted it can still impact on your security. So regular testing is essential, especially after deploying new systems and technologies and as a part of your security continual improvement lifecycle.
Penetration Testing
Leave it to our team of expert penetration testers to identify vulnerabilities in your environment.
Our tailored assessments can cover every aspect of network security from general vulnerability identification to fully exploiting vulnerable web applications.
The Top Cyber Threats in Fintech and How to Reduce Cyber Risk
Securing the Future of Financial Technology: Navigating Cyber Security Challenges in a Rapidly Evolving Landscape
The finance sector is one of the biggest targets of cyber threat actors with 65% of organisations hit by ransomware in 2024, according to recent research by Sophos. As the financial technology (Fintech) sector continues to revolutionise the way we handle money, the stakes for cyber security have never been higher.
The integration of innovative digital solutions, from AI-driven financial services to blockchain technology, has opened up new opportunities for growth, but it has also expanded the threat landscape.
This blog explores the current cyber security challenges facing the financial technology industry, the impact of these threats, and the best practices that companies can adopt to safeguard their operations and customer trust.
The Rising Threats in Fintech: A Snapshot of Today’s Cyber Security Landscape
The Fintech industry, characterised by its rapid adoption of cutting-edge technologies, is a prime target for cybercriminals. According to recent reports, the financial services sector experiences cyber-attacks 300 times more frequently than other industries, with Fintech companies being particularly vulnerable due to their digital-first nature. The rise of AI and machine learning in Fintech has further complicated the threat landscape, as these technologies can be both a tool for defence and an instrument for sophisticated attacks.
Key Threats Facing Fintech Today
- Data Breaches: With vast amounts of sensitive financial data at stake, data breaches remain one of the most significant risks for Fintech and financial services firms. Recent breaches, such as the SolarWinds attack, have highlighted the vulnerabilities in supply chains and third-party providers, making it clear that no organisation is immune.
- AI-Driven Cyber Attacks: The same AI technologies that enable personalised financial services are also being used by cybercriminals to automate attacks, enhance phishing campaigns, and exploit vulnerabilities faster than traditional methods. For instance, AI can create highly convincing deepfake videos and emails, making it easier to deceive even the most vigilant employees.
One of the most alarming examples occurred in earlier this year, when cybercriminals targeted a Hong Kong-based financial services firm in a first-of-its-kind heist. Using advanced deepfake technology, the attackers impersonated the firm’s Chief Financial Officer (CFO) during a video conference call. They convincingly replicated the CFO’s voice and appearance, deceiving an employee into transferring nearly £20 million to a fraudulent account. [source: Ars Technica] - Regulatory Challenges: With evolving regulations such as GDPR and PSD2 in Europe, and new guidelines from the FCA and other financial authorities worldwide, Fintech companies must navigate a complex web of compliance requirements. Failure to comply not only risks legal substantial penalties, but also damages brand reputation.
The Future of Fintech Security
Quantum Computing
The Fintech industry faces a significant challenge with the advent of quantum computing, particularly regarding encryption. As quantum technology advances, traditional cryptographic methods could become obsolete, necessitating a costly overhaul of encryption standards. The transition to quantum-resistant encryption is crucial for maintaining data security but will require significant investment and regulatory adjustments across the global Fintech sector. According to a recent report by Moody’s Ratings “Quantum computing’s threat to asymmetric encryption is currently mitigated by challenges in error correction, scalability, talent shortages and limited computing power…” However, quantum computing could break asymmetric encryption within 5 to 30 years. [source: Fintech Magazine]
The Global Treasurer predicts that quantum computing will revolutionise the Financial Services and Fintech industries, particularly in financial modelling, analysis, payment systems and cyber security. Financial institutions will need to adopt quantum-resistant algorithms, shifting towards more dynamic and adaptive security strategies. This evolution will require collaborative efforts across the global financial sector, including international cooperation, to build resilient global payment systems, enforce standardised regulations, and ensure a secure, efficient future leveraging quantum technology.
Compliance and regulations in quantum computing is not just becoming central to cyber security in Financial Services, but also to ensuring market viability. The Director of Quantum at KPMG, Michael Egan states that “While quantum technologies are rapidly developing, the threat of ‘Harvest now, Decrypt later’ is real and immediate. With increasing legislation, together with long procurement and mitigation cycles, there is a need to act now.” [source: KPMG]
The Role of Compliance and Regulatory Standards in Strengthening Cyber Defences
Compliance with industry standards is not just a legal obligation; it is a critical component of a robust cyber security strategy. Frameworks such as ISO/IEC 27001 and guidelines from regulatory bodies like the FCA in the UK provide a structured approach to managing sensitive data and mitigating risks.
Key Compliance Measures for Fintech
- Data Protection Compliance: Ensuring adherence to FCA, GDPR and other data privacy and financial authority regulations is essential for protecting customer data, and arguably the integrity of Fintech and Financial Services industries. This includes implementing robust data encryption, conducting regular audits, and maintaining clear data governance policies.
- PSD2 and Open Banking: With the advent of open banking, Fintech companies must ensure that their APIs are secure, and that customer consent is properly managed. Compliance with PSD2 not only protects consumer data but also enhances trust in digital financial services.
- Adoption of Cyber Security Frameworks: Leveraging established cyber security frameworks like NIST, ISO/IEC 27001 or the Cyber Essentials scheme in the UK can help Fintech firms standardise their security practices and stay ahead of emerging threats.
Best Practices for Cyber Security in Fintech
To navigate the complex cyber security landscape, Fintech companies must adopt a proactive approach. Here are some best practices that should be integral to any Fintech firm’s cyber security strategy:
- Regular Penetration Testing and Red Teaming: Penetration testing and red teaming exercises are crucial for identifying vulnerabilities before attackers can exploit them. By simulating real-world attacks, these practices allow Fintech companies to evaluate their security posture and improve their defences.
- Managed Detection and Response (MDR): MDR services provide continuous monitoring and analysis of an organisation’s security environment. By outsourcing to experts, Fintech firms can ensure that threats are detected and mitigated in real-time, reducing the risk of a successful attack.
- Incident Response and Recovery: Having a robust incident response plan is essential for mitigating the damage caused by cyber incidents. Fintech companies should invest in both in-house and outsourced incident response teams to ensure a swift and effective reaction to breaches.
- Employee Training and Awareness: Employees are often the first line of defence against cyber threats. Regular training sessions on phishing, social engineering, and secure data handling can significantly reduce the risk of human error leading to a security breach.
- Vulnerability Management: Regularly updating and patching software, coupled with continuous vulnerability assessments, is vital for maintaining a secure infrastructure. Cyber security as a Service (CSaaS) solutions, such as HackRisk, can help Fintech companies manage vulnerabilities effectively without overburdening internal teams.
Building a Resilient Cyber Security Strategy in Fintech
As Fintech continues to reshape the financial services landscape, the importance of cyber security cannot be overstated. By understanding the current threats, complying with regulatory standards, and implementing best practices, Fintech companies can build a resilient security posture that not only protects their operations but also fosters trust with their customers.
Free Posture Assessment
Understand your security risks and how to fix them.
Take the first step to improving your cyber security posture, looking at ten key areas you and your organisation should focus on, backed by NCSC guidance.
Claim your free 30-minute guided posture assessment with a CyberLab expert.








