Quick Wins to be Cyber Secure
Jack Smallpage, Information Security Officer at CyberLab, explains five simple things you can do to protect your business and improve your cyber security.
-
- Mobile Device Management
-
- Email Security
-
- Keeping your systems up to date
-
- Passwords
-
- Cyber Awareness
-
- Free Security Consultation
Cyber security is a broad subject with hundreds of do’s and don’t’s and can often be a daunting challenge. However, there are core pillars you can focus on easily to boost your business’ security. The tips below should provide you with some easy actions to help you take the first steps to become cyber secure!
Mobile Device Management
Smartphones and tablets can be just as powerful as traditional computers but leave the safety of the office/home far more frequently.
-
- Identify what your people’s mobile devices can potentially access.
- Devices may sync with the company’s OneDrive or Teams to access files and conversations. Even basic email access exposes the phone to information and attachments that we all have scattered within our mailbox.
- Identify what your people’s mobile devices can potentially access.
-
- Make sure that any device that has access to your business’ data is secured and controlled.
- Solutions such as Microsoft’s Intune or Sophos Mobile can help manage your mobile devices, control what data is available to your people and how that data is used.
- Make sure that any device that has access to your business’ data is secured and controlled.

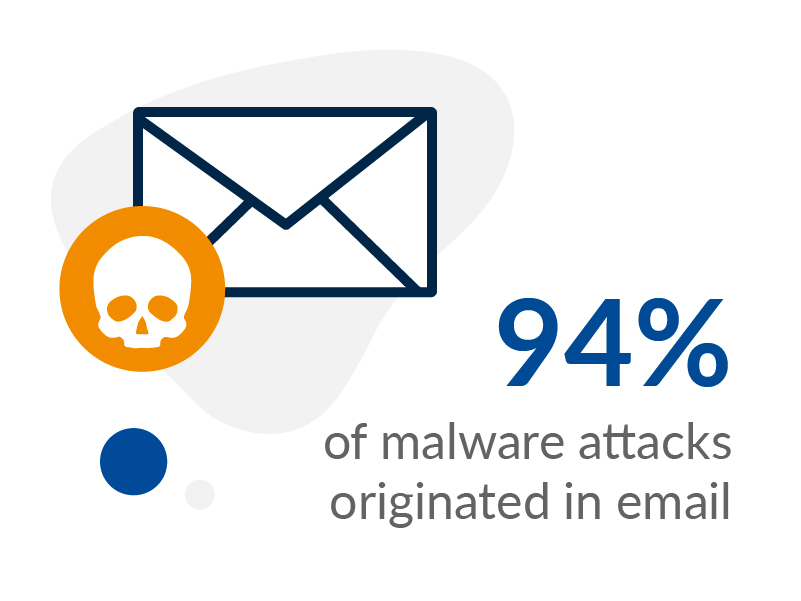
Email Security
“Phishing is when attackers attempt to trick users into doing ‘the wrong thing’, such as clicking a bad link that will download malware, or direct them to a dodgy website.”
Source: National Cyber Security Centre
Phishing remains the most common threat vector in the 2021 Cyber Security Breaches Survey. So it is no surprise that all businesses, big and small, are almost guaranteed to receive phishing attacks at some point. Help keep your people safe with the following:
Phishing remains the most common threat vector in the 2021 Cyber Security Breaches Survey. So it is no surprise that all businesses, big and small, are almost guaranteed to receive phishing attacks at some point. Help keep your people safe with the following:
-
- Give as little access as possible
- Configure your people’s accounts using the ‘least privilege’ principle. A compromised admin account can cause untold damage while a ‘least privilege’ user can help restrict malicious actions after compromise.
- Give as little access as possible
-
- Educate your people
- Here’s four things Mimecast recommend to look for:
-
- Look for inconsistencies in links, addresses and domains.
-
- Watch out for bad spelling and grammar and unfamiliar language.
-
- Be suspicious of demands for urgent action.
-
- Be wary of attachments.
-
- Here’s four things Mimecast recommend to look for:
- Educate your people
-
- Have an easy method for reporting suspected emails and investigating them.
- For those that are able to, Microsoft 365’s Phishing Investigation tool offers a great reporting and automated investigation function with proactive phishing detection and protection which can help take some strain off your technical / security people while making it easier for your end users. However, for those wanting a more basic approach, a simple process combined with proper end-user training can also suffice. Try including frequently asked questions in your process to help your users such as:
-
- What do we report? (Do you want them to report all suspected phish or simply delete them)
-
- Who do we report to? (Who should handle these phish reports or questions)
-
- How do we report? (How should your users forward their suspected phishing to you)
-
- For those that are able to, Microsoft 365’s Phishing Investigation tool offers a great reporting and automated investigation function with proactive phishing detection and protection which can help take some strain off your technical / security people while making it easier for your end users. However, for those wanting a more basic approach, a simple process combined with proper end-user training can also suffice. Try including frequently asked questions in your process to help your users such as:
- Have an easy method for reporting suspected emails and investigating them.
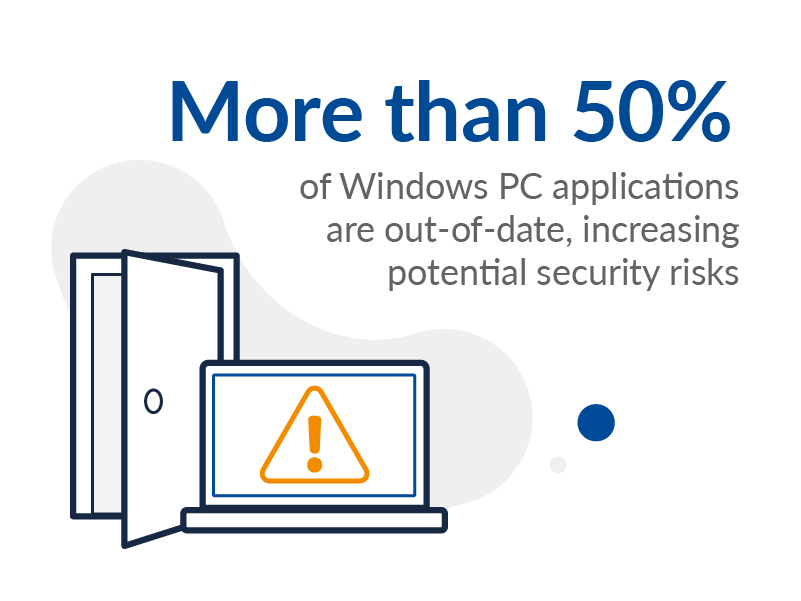
Keep your systems and software up to date!
-
- Know what IT equipment is on your network and what software is installed on each device.
-
- Ensure all software and firmware are kept up to date with the latest versions
- This is also known as patching.
- Where possible and available, systems should be set to ‘automatically update’ with patches being installed within 14 days of release as a rule of thumb.
- Ensure all software and firmware are kept up to date with the latest versions
With over 20,000 vulnerabilities (CVE’s) reported in 2021 alone, reinforce your patching regime with adequate vulnerability assessment and management to help identify systems and areas that may have been forgotten or missed – we’re only human after all!
Know when products on your network reach their ‘end of support’ date and no longer receive security updates. In such cases, you should strongly consider replacing the product with a modern alternative, especially for those which are internet facing.
Passwords
To make sure you’re making the most of passwords within your business, consider the following:
-
- Use two-factor authentication (2FA),
- This requires a user to provide an additional action (usually a code via their smartphone) before gaining access to the account. This should be applied as widely as possible, but it’s particularly important for admin and internet-facing accounts.
- Use two-factor authentication (2FA),
-
- Make sure to give your people guidance on setting secure passwords and ensure your systems enforce these requirements wherever possible.
-
- Password managers provide a secure way for your people to create and store their passwords via a ‘master’ password.
- The master password itself must be strong and should support 2FA or similar to ensure the vault is secure. Give your people a fighting chance by helping with the large amounts of passwords they deal with!
- Password managers provide a secure way for your people to create and store their passwords via a ‘master’ password.
-
- Stop enforcing regular password changes
- This helps users choose more secure passwords than weaker ones with repetitive sequences. Instead, you should only need to change passwords when you suspect they have been compromised.
- Stop enforcing regular password changes
Cyber Awareness
One of the most effective wins to becoming cyber secure is your people’s training and security culture. All the processes and measures in the world can be useless if the user doesn’t know how to use them properly.
Your people must report any phishing and security incidents as soon as possible and feel safe to ask for help if unsure (even if they have already clicked). Punishing people for getting caught out only discourages them and others from reporting in the future, causing delayed response or even no response at all resulting in greater harm to your business in the long run.
Detect. Protect. Support.
Posture Assessment
Understand your security risks and how to fix them.
Take the first step to improving your cyber security posture, looking at ten key areas you and your organisation should focus on, backed by NCSC guidance.
Claim your free 30-minute guided posture assessment with a CyberLab expert.


Leave a Reply
You must be logged in to post a comment.